You're sitting in a board meeting, and someone drops the bombshell – your Azure bill has skyrocketed by 40% this quarter, and oh, there was also a minor security incident last week. Sound familiar? Well, you're not alone. I've been architecting Azure solutions for over 5 years, and I can tell you that this scenario plays out in enterprises more often than you'd think.
Here's the kicker: As compared to Q1 of 2023, DDoS attacks increased by 50% year-over-year in 2024 alone, making it crystal clear that security isn't just another checkbox – it's your business lifeline. Meanwhile, cloud costs continue their relentless march upward, with many organizations unknowingly burning cash on idle resources and oversized VMs.
But what if I told you that security and cost optimization aren't opposing forces? What if they're actually dance partners, moving in perfect harmony to create a lean, mean, cloud-fighting machine? That's exactly what we're diving into today.
Why Azure Security and Cost Optimization Matter More Than Ever

Let me share something that might surprise you: According to a recent study, 80% of companies experienced at least one cloud security incident in the last year. That's 4 out of 5 companies dealing with breaches, data leaks, or unauthorized access. And here's where it gets interesting – these security incidents don't just threaten your data; they devastate your budget with recovery costs, compliance fines, and reputation damage.
On the flip side, I've seen companies waste thousands of dollars monthly on:
- Ghost VMs running 24/7 without anyone using them
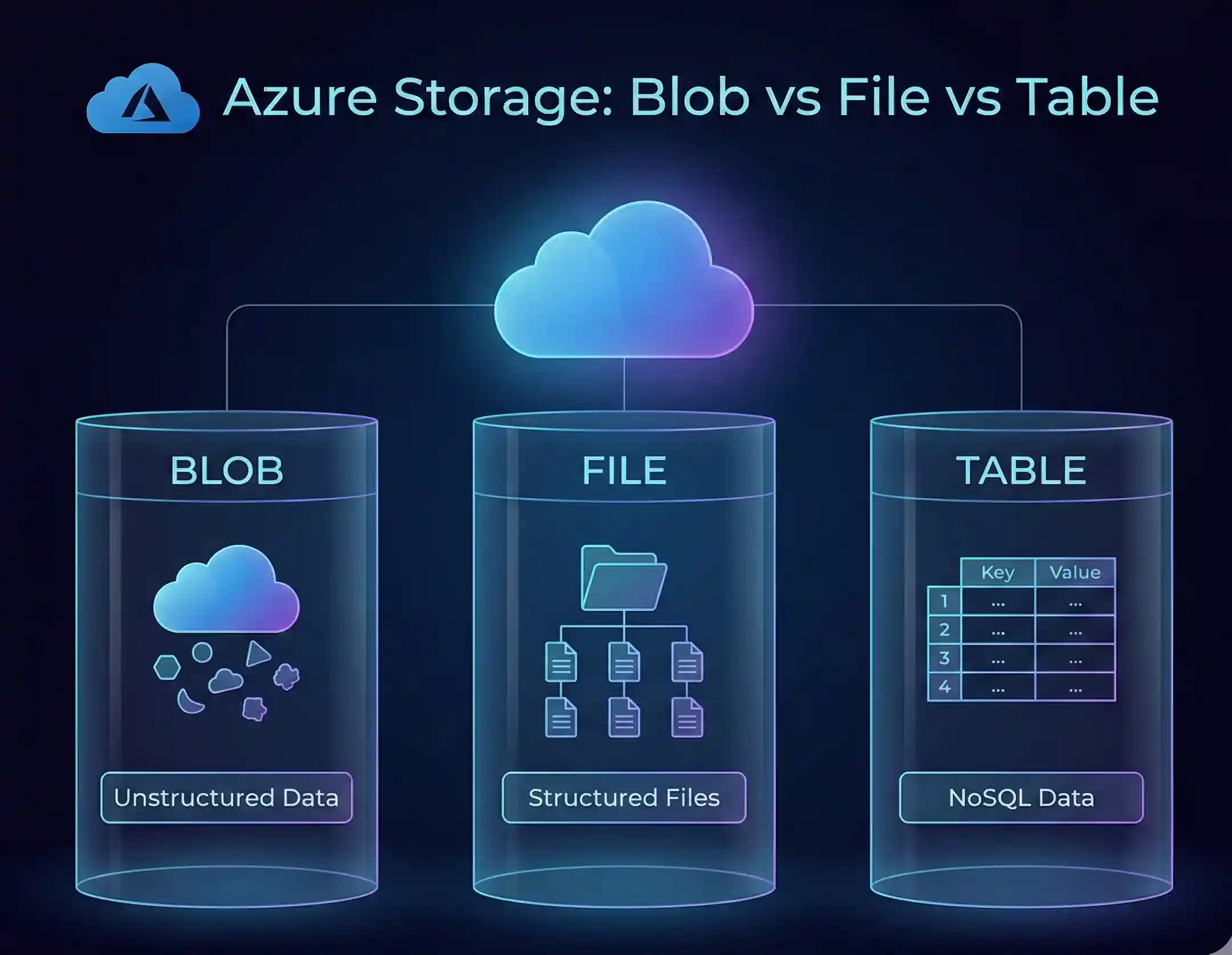
- Premium storage tiers for data accessed once a year
- Oversized instances running at 5% capacity
- Untagged resources that nobody can trace back to a project
The beautiful part? When you implement smart security practices, you often discover cost-saving opportunities, and vice versa. It's like finding money in your winter coat pocket – unexpected but delightful!
The Shared Responsibility Model: Your First Reality Check
Before we dive into the practices, let's get one thing straight – Azure security is a team sport. Microsoft handles the infrastructure, but you're the goalkeeper for your data and applications. Think of it like renting an apartment: the landlord maintains the building structure, but you're responsible for locking your door and not leaving valuables on the balcony.
Here's how it breaks down:
IaaS (Infrastructure as a Service): You're basically the DIY enthusiast here. Microsoft provides the hardware and hypervisor, but you handle the OS, applications, and data security.
PaaS (Platform as a Service): It's like having a partially furnished apartment. Microsoft manages more of the stack, but your applications and data are still your responsibility.
SaaS (Software as a Service): Microsoft does the heavy lifting, but you still need to manage user access and data classification.
Practice #1: Lock Down Identity Like Fort Knox (But Smarter)
The Multi-Factor Authentication (MFA) Revolution

Remember when passwords were enough? Yeah, those days are as dead as dial-up internet. Multi-factor authentication helps you add an extra security layer to your account and can block 99% of account attacks.
How I implement MFA in my projects:
- Start with the admins – If hackers compromise an admin account without MFA, it's game over
- Roll out to all users – Yes, even Bob from accounting who "doesn't do anything important"
- Use Conditional Access – Require MFA based on location, device, or risk level
Cost Impact: Basic multifactor authentication features are available to Microsoft 365 and Microsoft Entra ID users and administrators for no extra cost.
Role-Based Access Control (RBAC): The Art of Least Privilege

I once worked with a company where everyone was basically an admin. It was like giving everyone in your office a master key – convenient until someone loses it. Give users the least access they need. Don't make everyone an admin.
My RBAC Strategy:
- Create role definitions that match actual job functions
- Use Azure AD Privileged Identity Management (PIM) for just-in-time access
- Review permissions quarterly (set a calendar reminder, seriously)
Money-Saving Tip: Proper RBAC prevents accidental resource creation. I've seen developers spin up expensive VMs for testing and forget about them. With proper roles, this becomes impossible.
Practice #2: Embrace Zero Trust Architecture (Trust No One, Verify Everything)

The world has changed. The next Azure security best practices include no longer trusting anything by default. Zero Trust isn't paranoia; it's pragmatism.
Implementing Zero Trust Without Breaking the Bank:
- Verify explicitly – Every access request gets checked, even from your CEO
- Use least privilege access – Just-in-time, just-enough permissions
- Assume breach – Design your architecture as if hackers are already inside
Real-world example: I helped a financial services client in Sri Lanka and Asia Region implement Zero Trust. They discovered 40% of their users had excessive permissions they never used. Cleaning this up not only improved security but also reduced their Azure AD Premium license requirements by 30%.
Practice #3: Master Azure Cost Management Like a CFO
Azure Advisor: Your Free Financial Consultant

Azure Advisor helps you optimize and improve efficiency by identifying idle and underutilized resources. It's like having a personal trainer for your cloud spend.
My Weekly Azure Advisor Routine:
- Monday: Check for rightsizing recommendations
- Wednesday: Review security suggestions
- Friday: Analyze cost optimization proposals
Tagging: The Unsung Hero of Cost Control
Without tags, tracking Azure costs is like finding a specific grain of sand on a beach. Organizations are adopting more granular cost allocation techniques, leveraging Azure's expanded tagging capabilities.
Essential Tags I Always Use:
- Environment: Dev/Test/Prod
- Owner: Who's responsible
- Project: Which initiative
- CostCenter: Who's paying
- ExpiryDate: When to review/delete
Pro Tip: Enforce tagging policies through Azure Policy. No tag? No resource creation. It's tough love that saves thousands.
Practice #4: Reserved Instances and Savings Plans (The Art of Commitment)
Here's where things get juicy. You have the freedom to choose the savings options that best align with your workload patterns.

Reserved Instances: When You Know What You Want
Think of Reserved Instances like buying a yearly gym membership instead of daily passes. The 72% savings is based on one M32ts Azure Virtual Machine for the Windows OS in the East region running for 36 months.

When to use RIs:
- Stable, predictable workloads
- Production databases that run 24/7
- Core application servers
Savings Plans: Flexibility is King
Azure Savings Plans for Compute is an easy and flexible way to save on your compute costs compared to pay-as-you-go prices by committing to spending a certain hourly amount for 1 or 3 years. Savings can reach up to 65%.

Perfect for:
- Multi-region deployments
- Workloads that might scale up or down
- Organizations still figuring out their cloud strategy
My Warning: If you choose the Azure Savings Plan, remember that it commits you to paying a fixed hourly amount, whether you use the resources or not.
My Rule of Thumb: Start with Savings Plans for flexibility, then transition stable workloads to Reserved Instances for maximum savings.
Practice #5: Network Security That Doesn't Break the Bank
Network Security Groups (NSGs): Your Virtual Bouncers

NSGs are like bouncers at an exclusive club – they decide who gets in and who stays out. The best part? They're free!
My NSG Best Practices:
- Start with deny-all, then explicitly allow what's needed
- Use Application Security Groups for easier management
- Review rules monthly (outdated rules are security holes)
Azure Firewall vs. Third-Party Solutions
While Azure Firewall offers enterprise-grade protection, it can be pricey for smaller deployments. Here's my decision tree:
- Small deployments: NSGs + Azure DDoS Basic (free)
- Medium deployments: NSGs + Web Application Firewall
- Enterprise: Full Azure Firewall with threat intelligence
Practice #6: Microsoft Defender for Cloud (Your Security Command Center)

Microsoft Defender for Cloud is a cloud-native application platform (CNAPP) with a set of security measures and practices to protect your cloud-based applications from cyberthreats and vulnerabilities.
Getting Started Without Overwhelming Your Budget:
- Start with the free tier – Get security recommendations without spending a dime
- Enable selectively – Turn on paid features only for critical workloads
- Use the Secure Score – It gamifies security (who doesn't love a good score?)
Cost Optimization Trick: Use Defender's recommendations to identify and remove unused resources. I once found $3,00/month in forgotten test environments this way!
Practice #7: Smart Resource Management and Automation
Auto-Shutdown: Your After-Hours Money Saver
Dev/test environments running 24/7 are like leaving all lights on when you go on vacation – wasteful and unnecessary.
My Auto-Shutdown Setup:
- Dev environments: Shutdown at 7 PM, start at 7 AM
- Test environments: On-demand with auto-shutdown after 2 hours idle
- Production: Obviously, these stay on!
Potential Savings: 60-70% reduction in dev/test costs
Rightsizing: Goldilocks Would Be Proud
Azure Advisor monitors your virtual machine usage for seven days and then identifies underutilized virtual machines. VMs with CPU usage under 5% are flagged for rightsizing.
My Rightsizing Process:
- Run Azure Advisor recommendations monthly
- Test downsizing in dev first
- Monitor performance for a week
- Apply to production with a rollback plan
Practice #8: Azure Key Vault (Your Digital Safe)

Hardcoding secrets in your code is like hiding your house key under the doormat – everyone knows to look there.
Key Vault Best Practices That Save Money and Headaches:
- Store all secrets, keys, and certificates centrally
- Use Managed Identities (no more password rotation!)
- Enable soft-delete (saved me from disaster twice)
Cost Tip: One Key Vault can serve multiple applications. Don't create one per app – that's like having 50 safety deposit boxes when one would do.
Practice #9: Monitoring and Alerting (Know Before It Blows)
Setting Up Cost Alerts:

Set up alerts for budget thresholds to prevent overspending. Here's my alert ladder:
- 50% of budget: "Hey, we're halfway there"
- 75% of budget: "Time to review what's happening"
- 90% of budget: "All hands on deck!"
- 100% of budget: "Houston, we have a problem"
Security Monitoring That Matters:
Focus on alerts that indicate real threats:
- Multiple failed login attempts
- Privilege escalations
- Resources created outside approved regions
- Unusual data transfer patterns
Practice #10: Compliance and Governance (The Boring Stuff That Saves Your Job)
Azure Policy: Your Automated Enforcer
Think of Azure Policy as your cloud's constitution – it sets the rules everyone must follow.
Policies I Always Implement:
- Require tags on all resources
- Restrict VM sizes to approved list
- Enforce encryption on storage accounts
- Block public IP creation in production
Compliance Manager: Your Audit Buddy
Whether it's GDPR, HIPAA, or PCI-DSS, Compliance Manager helps you track your compliance posture. It's like having a compliance consultant on retainer, minus the hefty fees.
Bringing It All Together: Your 90-Day Action Plan

Days 1-30: Foundation
- Enable MFA for all users
- Set up basic tagging strategy
- Configure cost alerts
- Review and clean up unused resources
Days 31-60: Optimization
- Implement auto-shutdown for dev/test
- Analyze Reserved Instance opportunities
- Configure NSGs properly
- Enable Azure Advisor recommendations
Days 61-90: Advanced
- Implement Zero Trust principles
- Set up advanced monitoring
- Configure Azure Policy
- Plan for Savings Plans or Reserved Instances
Real-World Success Story
Let me share a win from my recent consulting engagement. A SaaS company was spending around $5,600/month on Azure with serious security gaps. After implementing these practices:
Security Wins:
- Zero security incidents (down from 3 per quarter)
- Passed SOC 2 audit on first attempt
- Reduced privileged accounts by 80%
Cost Wins:
- 40% reduction in monthly spend
- Saved around $1200/month through rightsizing
- Additional around $1160/month saved via Reserved Instances
The IT manager literally called it "cloud magic." I call it smart engineering.
Common Pitfalls to Avoid
- All-or-nothing mentality – Start small, iterate, improve
- Ignoring the basics – MFA and tagging aren't sexy, but they're essential
- Set and forget – Cloud optimization is a journey, not a destination
- Over-engineering – Not every workload needs enterprise-grade everything
- Under-communicating – Keep stakeholders informed about changes
Certifications That Level Up Your Game
Want to become an Azure security and cost optimization ninja? Consider these certifications:
- Microsoft Azure Fundamentals (AZ-900) – Start here if you're new
- Azure Security Engineer (AZ-500) – Deep dive into security
- Azure Administrator (AZ-104) – Master day-to-day operations
- Azure Solutions Architect (AZ-305) – Design secure, cost-effective solutions
FAQs: Your Burning Questions Answered
What are the best practices for optimizing Azure costs while ensuring security?
Start with the fundamentals: implement MFA and RBAC for security, then layer in cost optimization through Reserved Instances, auto-shutdown policies, and regular rightsizing reviews. Remember, many security features like NSGs are free, so use them liberally!
How does Azure Security Center help with cost optimization and threat protection?
Microsoft Defender for Cloud serves as a security centre that monitors your overall security posture. It shows your security state, what to improve, and how to do that. It also helps identify unused resources that can be eliminated for cost savings.
What native Azure tools assist with cost management and security compliance?
Azure Advisor, Cost Management, Azure Policy, and Microsoft Defender for Cloud are your core toolkit. They're integrated, mostly free at basic tiers, and provide actionable insights for both security and cost optimization.
How can I use Azure Hybrid Benefit to save on license and security costs?
If you have existing Windows Server or SQL Server licenses with Software Assurance, Azure Hybrid Benefit can save you up to 85% when combined with Reserved Instances. It's like trading in your old car for credit on a new one!
What is the role of Azure Advisor in balancing cost optimization and security?
Azure Advisor is your Swiss Army knife – it provides recommendations for cost, security, performance, and operational excellence all in one place. Follow its suggestions religiously for the first few months.
How do reserved instances and spot VMs help reduce Azure costs?
Reserved Instances offer up to 72% savings for predictable workloads, while Spot VMs can save up to 90% for interruptible workloads. Use RIs for production, Spot VMs for batch processing and testing(Limited time tasks).
What are common security risks to consider when optimizing Azure infrastructure costs?
The biggest risk is cutting security corners to save money. Never disable logging, skip backups, or ignore patches to reduce costs. These "savings" become expenses when (not if) something goes wrong.
How can I implement identity and access management (IAM) securely and cost-effectively on Azure?
Start with Azure AD free tier, implement MFA (included), use built-in roles before creating custom ones, and leverage Managed Identities to eliminate password management overhead.
What automation options are available for Azure cost and security optimization?
The Azure Automation, Logic Apps, and Azure Functions can automate everything from resource shutdown to security remediation. Start with simple automation like auto-shutdown, then gradually add complexity.
How can monitoring and alerts improve both security posture and cost control in Azure?
The Monitoring is your early warning system. Set up alerts for unusual spending patterns (possible resource hijacking) and security events. The faster you know, the less it costs to fix.
The Bottom Line: Security and Savings Go Hand-in-Hand
Here's what I want you to remember: securing your Azure environment and optimizing costs aren't competing priorities – they're complementary strategies that make each other stronger. Every unused resource you eliminate is one less attack surface. Every security automation you implement reduces manual overhead and human error.
Start with one practice from this guide. Just one. Implement it, measure the impact, then move to the next. In 90 days, you'll have a more secure, cost-effective Azure environment that would make any CTO proud and any CFO smile.

The cloud isn't about spending less or being more secure – it's about spending smart while being secure. And with these practices in your toolkit, you're ready to master both.
Remember, as I always tell my clients: "In the cloud, the only constant is change. Embrace it, automate it, and optimize it."
Now go forth and build that Azure fortress – one that's both impenetrable and economical. Your future self (and your budget) will thank you!
Ready to transform your Azure environment? Start with enabling MFA today – it takes 10 minutes and could save your company from a devastating breach. Then download Azure Advisor recommendations and pick one cost optimization to implement this week. Small steps lead to giant leaps in cloud excellence.
What's your biggest Azure challenge – security or cost? Drop a comment below and let's solve it together!






No comments yet. Be the first to share your thoughts!