The Big Question Every Cloud Architect Faces
You're building a web application for your company. Everything looks good. But then comes the million-dollar question:

Trust me, I've been there. As someone who has spent the past five years designing Azure infrastructure solutions, this question pops up in almost every project. And here's the thing—there's no one-size-fits-all answer.
Both services look similar on paper. They're both Layer 7 load balancers. They both support WAF. They both handle HTTP and HTTPS traffic. So what's the real difference?
In this article, I'll explain everything you need to know. No fluff. No corporate jargon. Just practical insights that will help you make the right choice for your current specific situation. Whether you're a university student learning Azure or a seasoned developer, this article has something for you.
Let's dive in.
Quick Overview: What Are These Services?
Azure Front Door: Your Global Traffic Manager

Think of Azure Front Door as your application's global receptionist. It sits at Microsoft's edge network—hundreds of points of presence (PoPs) scattered across the globe. When a user from Tokyo tries to access your app, Front Door routes them to the closest healthy backend. Simple as that.
Front Door is a global service. It doesn't live in any specific Azure region. Instead, it operates everywhere at once. This makes it perfect for applications that serve users worldwide.
Key capabilities include CDN-like caching, SSL offload, URL-based routing, and built-in DDoS protection. You also get latency-based routing, which automatically sends users to the fastest available backend.
Azure Application Gateway: Your Regional Traffic Controller

Application Gateway, on the other hand, is more like a skilled traffic police man at a busy junction. It's a regional service. You deploy it in a specific Azure region, and it handles traffic within that region.
This service excels at granular control. Need to route /api requests to one backend pool and /images to another? Application Gateway does that brilliantly. It can also balance traffic between individual VMs or app service within your virtual network.
Here's something cool: Application Gateway supports connection draining, session affinity to specific servers, and direct integration with Azure Kubernetes Service (AKS). These features matter a lot for enterprise applications.

Best practice → To avoid bypassing the gateway, we should lock down the App Service public endpoint using Access Restrictions or Private Endpoint. That way, only traffic coming through Application Gateway is allowed.
Global vs Regional: The Core Difference
This is the fundamental distinction you need to understand. Let me explain what it means in practice.
Azure Front Door operates globally. It uses Microsoft's anycast network to route traffic. When your user in London makes a request, Front Door intercepts it at the nearest edge location. It then decides which backend region should handle that request. The whole process happens in milliseconds.
Application Gateway operates regionally. It lives inside a specific Azure region. It handles traffic that's already arrived at that region. Think of it as the internal routing system within your local data center.
Why does this matter? If your application runs in multiple regions, Front Door can automatically failover between them. Application Gateway can't do that on its own. You'd need to combine it with Azure Traffic Manager for global failover.
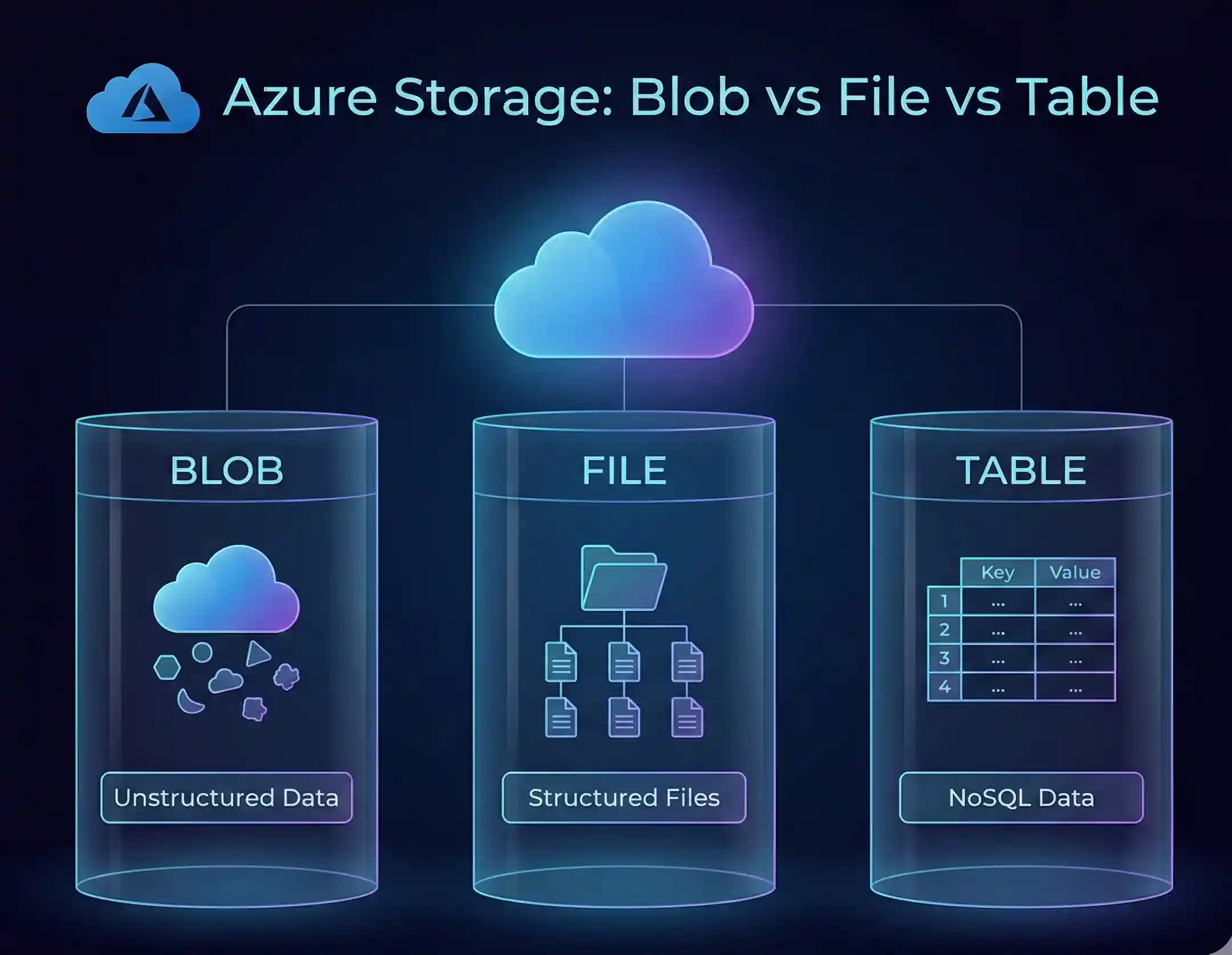
Head-to-Head Comparison Table
Let's look at the key differences side by side:
| Feature | Azure Front Door | Application Gateway |
| Scope | Global | Regional |
| OSI Layer | Layer 7 (HTTP/HTTPS) | Layer 7 (HTTP/HTTPS) |
| Load Balancing | Across regions/clusters | VMs/app service in VNet |
| CDN Caching | Yes, built-in | No |
| WAF Support | Yes (Premium tier) | Yes (WAF v2 SKU) |
| SSL Offload | Yes | Yes |
| Session Affinity | To region/cluster | To specific server |
| Connection Draining | No | Yes |
| Private Link Support | Yes (Premium tier) | Yes |
| VNet Integration | Via Private Link only | Native support |
| Health Probes | Latency + health based | Health based only |
Performance and Latency: Who Wins?

Here's where things get interesting. Performance depends heavily on your use case.
Azure Front Door Performance
Front Door uses split TCP and anycast routing. What does that mean? When a user connects, they hit the nearest edge location. That edge location maintains a persistent, optimized connection to your backend. The result? Faster handshakes and reduced latency.

For global applications, this is a game-changer. I've seen latency improvements of 30-50% for users far from the backend region. Azure Front Door also does dynamic site acceleration, which optimizes the route between edge and origin.
The caching layer adds another performance boost. Static assets like images, CSS, and JavaScript files get served directly from edge locations. Your backend never even sees those requests.
Application Gateway Performance
Application Gateway shines in scenarios where traffic stays within a region. It offers predictable, low-latency routing to backend pools. There's no global network hop—just direct communication within your VNet.

Autoscaling is another strength. Application Gateway v2 automatically adjusts capacity based on traffic load. This means consistent performance during traffic spikes without manual intervention.
My recommendation: Use Front Door for global apps with users worldwide. Use Application Gateway for regional apps where traffic doesn't need to cross continents.
Security Showdown: WAF and DDoS Protection
Security is non-negotiable. Both services offer strong protection, but they implement it differently.
Azure WAF on Front Door

Front Door Premium includes WAF at no additional cost. That's a big deal. You get protection against OWASP top 10 vulnerabilities, bot management, and rate limiting—all baked in.
Because WAF runs at the edge, malicious traffic gets blocked before it even reaches your backend. This reduces load on your infrastructure and improves overall resilience. Front Door also includes built-in DDoS protection at the network edge. This must saving your time, money and headache.
Custom rules let you create specific policies. Want to block traffic from certain countries? Done. Need to rate-limit specific endpoints? Easy.
Azure WAF on Application Gateway

Application Gateway WAF v2 is mature and feature-rich. It supports the same OWASP rulesets and custom rules. The key difference? It protects traffic at the regional level.
One advantage Application Gateway has: it can integrate with Azure DDoS Protection Standard for enhanced protection. It also works seamlessly with Azure Security Center for centralized monitoring.
For internal applications that don't face the internet directly, Application Gateway WAF makes more sense. You get protection without the complexity of a global service.
Pro tip: You can actually use both together. Front Door provides edge security, while Application Gateway adds another layer of protection inside your region. Defense in depth at its finest.
Pricing Breakdown: What Will It Cost?
Let's talk money. This is often the deciding factor for many teams.

Azure Front Door Pricing
Front Door has two main tiers: Standard and Premium. Both use a combination of base fees, request charges, and data transfer costs.
- Standard tier: Great for content delivery and basic security. Lower base fee.
- Premium tier: Includes WAF, Private Link, and bot protection. Higher base fee but WAF is included.
The pricing model charges per request and per GB of data transfer. For high-traffic applications, costs can add up. However, Microsoft reports that Front Door Standard can be up to 45% cheaper than Front Door Classic for static websites.
Application Gateway Pricing
Application Gateway uses a different model. You pay for the gateway instance (fixed hourly cost) plus capacity units based on usage.
- Fixed cost: Charged hourly for the gateway instance.
- Capacity units: Based on compute, connections, and throughput consumed.
- WAF charges: Additional cost if you enable WAF policies.
For multi-region deployments, you need one Application Gateway per region. This multiplies your costs. A three-region deployment means three Application Gateway instances.
Which Is Cheaper?
It depends on your scenario:
- Single region, moderate traffic: Application Gateway usually wins.
- Multi-region, global users: Front Door can be more cost-effective because you only need one instance.
- High request volume: Front Door's per-request charges can get expensive.
Always use Azure's pricing calculator for your specific workload. Real numbers beat estimates every time.

Note: This screenshot was taken from the official Microsoft Pricing Calculator. It is used here for sample pricing demonstration purposes only. This image credits belong 100% to Microsoft Corporation.
When to Use Azure Front Door
Based on my experience, here are the scenarios where Front Door is the clear winner:
- Global applications: Users spread across multiple continents? Front Door is built for this.
- Multi-region failover: Need automatic failover between regions without DNS delays? Front Door handles it instantly.
- CDN requirements: Static content caching at edge locations improves performance dramatically.
- Modern web apps: SPAs, JAMstack sites, and microservices architectures benefit from Front Door's flexibility.
- API-first applications: Front Door works well with APIs that serve global consumers.
When to Use Application Gateway
Application Gateway makes more sense in these scenarios:
- Regional applications: Single-region deployments with local users don't need global routing.
- VNet-integrated workloads: Applications that need direct integration with virtual networks.
- Internal applications: Apps that don't face the public internet.
- Granular routing control: When you need to route traffic to specific VMs or containers.
- Connection draining needs: Graceful handling of ongoing connections during updates.
- AKS ingress: Application Gateway Ingress Controller (AGIC) provides native Kubernetes integration.
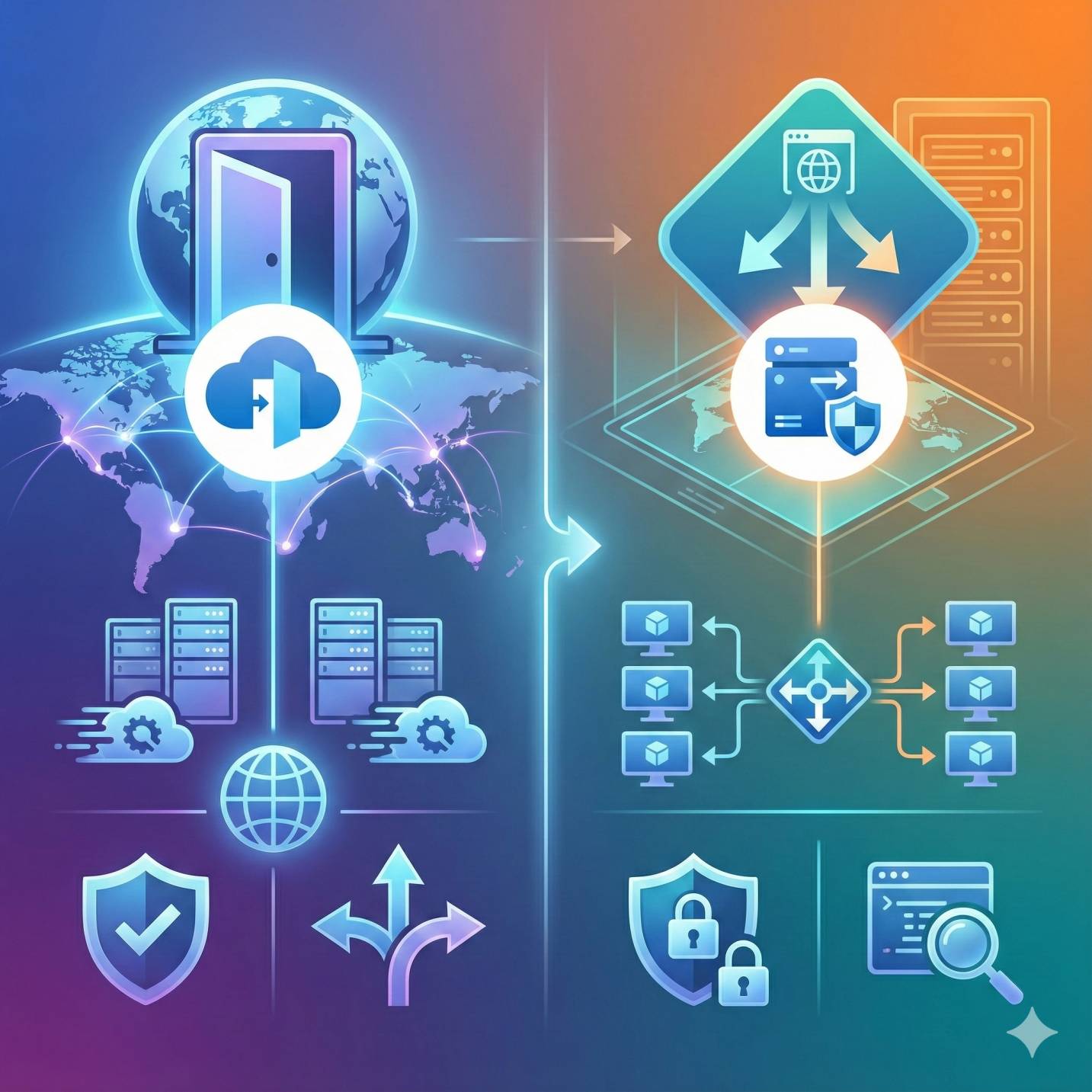
Reference Architecture: Using Both Together
Here's a secret that many architects miss: you don't have to choose. Using Front Door and Application Gateway together is a powerful design pattern.
How it works: Front Door sits at the global level, routing users to the nearest region. Within each region, Application Gateway provides fine-grained load balancing and additional security.
This architecture gives you the best of both worlds:
- Global load balancing and failover via Front Door
- Regional traffic management via Application Gateway
- Two layers of WAF protection
- CDN caching at the edge
- Connection draining for graceful deployments
I've implemented this pattern for some enterprise clients. It's particularly useful when you have complex routing requirements within each region but also need global reach.

Note: This architecture diagram was prepared based on my previous experience and knowledge. There can be multiple approaches for implementing this setup, and this is not the only method.
Frequently Asked Questions
1. What is the difference between Azure Front Door and Azure Application Gateway?
The main difference is scope. Front Door is a global service that routes traffic across regions using Microsoft's edge network. Application Gateway is a regional service that balances traffic within a specific Azure region. Both are Layer 7 load balancers, but they serve different architectural purposes.
2. Can I use Azure Front Door and Application Gateway together?
Absolutely! This is actually a recommended architecture for complex applications. Front Door handles global routing and edge caching, while Application Gateway manages regional traffic distribution. You get layered security and the strengths of both services.
3. Which is more cost-effective: Front Door or Application Gateway?
It depends on your deployment. For multi-region applications, Front Door is often cheaper because you only need one instance. For single-region apps with lower traffic, Application Gateway typically costs less. Always model your specific workload in the Azure pricing calculator.
4. Which service has better WAF capabilities?
Both offer similar WAF features with OWASP rulesets and custom rules. Front Door Premium includes WAF at no extra cost and blocks threats at the edge. Application Gateway WAF integrates better with regional security services. For maximum protection, use both.
5. Is Azure Front Door global and Application Gateway regional?
Yes, exactly. Front Door operates globally across all Azure edge locations. Application Gateway must be deployed in a specific Azure region and only handles traffic within that region.
6. Which should I choose for multi-region deployments?
Front Door is the natural choice for multi-region apps. It provides automatic failover, latency-based routing, and doesn't require multiple instances. Application Gateway alone can't do multi-region routing—you'd need to combine it with Traffic Manager.
7. What about internal or VNet-integrated applications?
Application Gateway is better suited here. It has native VNet integration and can be deployed as an internal load balancer. Front Door requires public endpoints by default (though Premium tier supports Private Link for secure origin connections).
8. How do performance and latency compare?
Front Door generally offers better latency for global users because of edge caching and optimized routing. Application Gateway provides consistent, low-latency routing within a region. Choose based on where your users are located.
Final Thoughts: Making Your Decision
So, which should you choose? Let me give you the simplified decision framework I use:
- Global users + multiple regions = Front Door
- Regional users + VNet integration = Application Gateway
- Complex enterprise + both requirements = Use them together
Remember, there's no wrong answer here. Both are excellent services. The right choice depends entirely on your specific requirements, budget, and architecture goals.
I hope this guide helped clarify the differences. If you're still unsure, start with your primary use case and scale from there. Cloud architecture is iterative—you can always adjust as your needs evolve.
Have questions? Drop a comment below or reach out on Linkedln. I'm always happy to discuss cloud challenges - Azure!
Ready to build your Azure architecture?
Check out the official Azure documentation for Front Door and Application Gateway.
Azure Front Door : https://learn.microsoft.com/en-us/azure/frontdoor/front-door-overview
Azure Application Gateway : https://learn.microsoft.com/en-us/azure/application-gateway/overview-v2





No comments yet. Be the first to share your thoughts!